Know what they know. Find it & fix it — across your cloud environment.
Modern attackers don’t wait for audits. They scan continuously for exposed services, weak configurations, and missing controls. Verdentify helps you understand what’s visible from the outside, validate what’s happening on the inside, and harden your cloud environments using proven security baselines.
This is practical cloud security — designed for growing teams, not enterprise overhead.
What We Secure
We focus on the control areas that matter most for real-world risk reduction and compliance alignment:
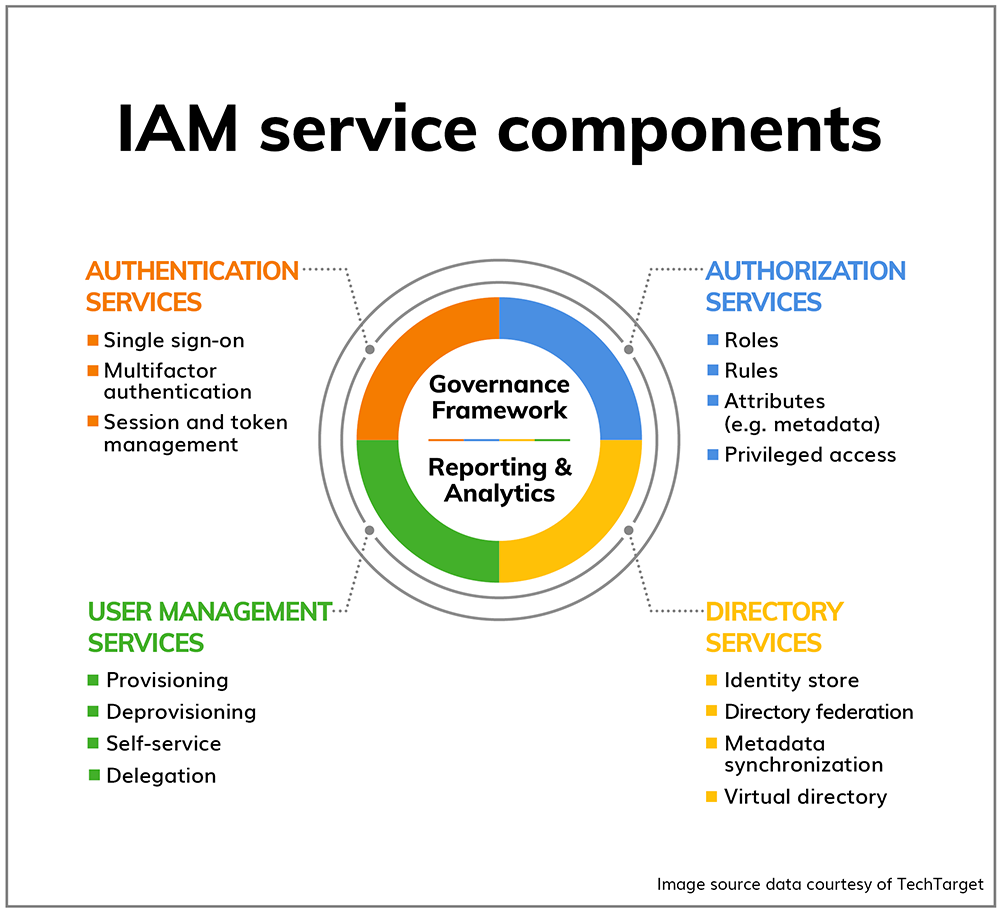
- Identity & access management
- Email and collaboration platforms
- Cloud infrastructure and configuration
- Logging, monitoring, and alerting
- Data protection

These areas form the foundation of both effective security programs and audit-ready environments.
Our Approach
Outside-in visibility meets inside-out hardening.
We start by understanding what attackers and automated scanners can already see about your environment. From there, we validate internal configurations against established security baselines and help you close the gaps that create the most risk.
Our approach is:
- Baseline-driven, not tool-driven
- Repeatable and auditable
- Designed to support compliance without becoming compliance theater
Platforms We Support
Verdentify provides cloud security assessments and hardening for the platforms most commonly used by startups and growing companies:
Microsoft 365 Security
Understand and reduce exposure across identity, email, collaboration, endpoints, and data.
Focus on configuration risk, attack surface reduction, and audit-aligned controls.
👉 Learn more about Microsoft 365 Security
Microsoft Azure Security
Secure subscriptions, resources, and identities while improving visibility and control across your Azure environment.
👉 Learn more about Azure Security
Amazon Web Services Security
Gain clarity into AWS configuration risk and security posture, then harden environments using proven best practices.
👉 Learn more about AWS Security
What You Get
Cloud security engagements typically deliver:
- Clear visibility into security exposure and risk
- Identified configuration gaps and weaknesses
- Prioritized remediation guidance
- Improved logging, monitoring, and alerting
- Documentation suitable for compliance and audit support
No vague reports. No unnecessary tooling. Just actionable security improvements.
How Cloud Security Supports Compliance
Strong cloud security is the foundation of compliance — not an afterthought.
Our cloud security work supports readiness and ongoing compliance efforts aligned to:
- NIST Cybersecurity Framework
- SOC 2
- ISO 27001
- HIPAA (when applicable)
By fixing real security issues first, compliance becomes a natural byproduct instead of a scramble.
When to Start with Cloud Security
Cloud security is a good fit if:
- You’re using Microsoft 365, Azure, or AWS
- You want to reduce real-world risk, not just check boxes
- You’re preparing for compliance readiness or Year 2+ audits
- You need clarity without hiring a full security team
Start with a Cloud Security Assessment
Whether you’re early in your security journey or refining a mature program, a cloud security assessment provides fast, actionable insight into where you stand — and what to fix next.
👉 CTA: Request a Cloud Security Assessment
